Alton Henley
Alton Henley is a higher education leader and technologist with over 36 years of combined military and civilian service. He most recently served as the college-wide Dean of Business at Montgomery College, where he also previously led the Information Technology Institute as Senior Director for 7 years. Alton spent two decades in the IT industry — including roles as a senior systems developer at Amtrak and assistant IT director at the University of Maryland, Baltimore — before dedicating himself to education. He is the creator of CodeWork Academy, a free grant-funded programming bootcamp in Maryland, and expanded Montgomery College’s Montgomery Can Code initiative by 200%. Alton has taught courses in web development, analytics, and cybersecurity, and his work centers on using experiential learning to equip students with practical, career-ready technology skills.
—
Presenting: Soft Targets: Why Small Municipalities Are Hackers’ Favorite Prey
Andre Piazza
Andre Piazza is a cybersecurity strategist with over two decades of experience translating complex technical trends into practical strategies. He specializes in predictive security frameworks, fraud prevention, and industry analyst relations. His background spans product strategy, engineering, and market influence, including pioneering 5 cybersecurity categories. Andre regularly speaks at industry events on cybersecurity strategy to grow awareness and build a more resilient security community.
—
Presenting: When Headlines Hit, They Strike: Predicting AI‑Driven News Scams
Andrew Bullen
Andrew Bullen leads the AI Security team at Stripe, where he designs infrastructural primitives that secure the company’s internal and customer-facing AI platforms. A ten-year veteran of Stripe, Andrew previously led the Data Platform and Privacy Engineering teams. He approaches security as a leadership challenge just as much as a technical one. His work sits at the intersection of engineering leadership, security, AI/ML, and usability. In addition to his technical work, Andrew is an engineering leadership coach and can be found online at andrewbullen.co.
—
Presenting: Breaking the Lethal Trifecta: Architectural Prompt Injection Defenses
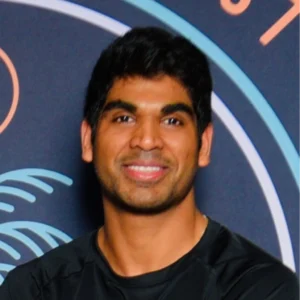
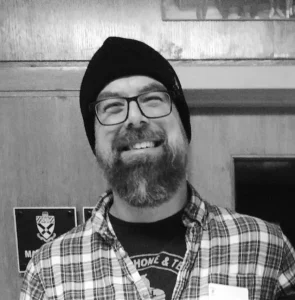
Anuj Soni
Anuj Soni is a Senior Reverse Engineer at the Johns Hopkins University Applied Physics Laboratory (APL) and the founder of The Malware Lab. With over 20 years of experience in malware reverse engineering and threat research, he has worked across government, security vendors, and consulting organizations, analyzing malicious code in support of incident response and threat research.
Anuj is the author of SANS FOR710: Advanced Code Analysis and co-author of FOR610: Malware Analysis Tools and Techniques, and previously served as a Senior Certified Instructor for the SANS Institute.
He also shares practical reverse engineering content on YouTube to help analysts sharpen their technical skills.
When Anuj is away from his keyboard, you’ll find him at the local gym, or with his kids (which is also a workout).
 sonianuj |
sonianuj |  asoni
—
Presenting: Malware Analysis Fundamentals: A Hands-On Workshop
asoni
—
Presenting: Malware Analysis Fundamentals: A Hands-On Workshop
Anurag Swarnim Yadav
Anurag Swarnim Yadav is a security researcher currently working on QubitAC, a platform focused on cryptographic discovery, inventory, and post-quantum cryptography (PQC) readiness. He holds a Ph.D. in Computer Science from the University of Florida, where his research centered on machine-learning–driven vulnerability detection and automated program repair.
—
Presenting: You Can’t Migrate What You Can’t See: Discovering Real Post-Quantum Crypto
Caleb Kinney
Caleb Kinney is a cybersecurity leader and Manager of Security Operations at Posit, where he leads security programs and focuses on making security risk measurable and actionable for platforms and open source projects used by millions of data scientists worldwide.
He contributes to Hacker Tracker, serves on the NumFOCUS Security Committee, and volunteers at DEF CON as a Goon. His work centers on turning security metrics into practical systems that reduce exposure and improve how teams prioritize risk.
Find his work at https://derail.net. Outside of security, he runs on Maryland back roads and explores with his wife and two daughters.
 cak
—
Presenting: Why Vulnerability MTTR Alone Misleads: Add MOVA to Measure Real Risk
cak
—
Presenting: Why Vulnerability MTTR Alone Misleads: Add MOVA to Measure Real Risk
Charles Adams
No information submitted.
—
Presenting: Hidden Exposure Crisis – How Supply Chain Leakage is Becoming the Norm
Chris Maenner
Chris is Head of Security at Ybor Technologies, where he focuses on securing Kubernetes platforms, AI workloads, and cloud-native infrastructure. He has been working in security engineering since 2006, spanning roles from early-stage startups to enterprise platform teams.
Chris serves as a board member of BSidesPhilly and is a frequent speaker at security conferences, including multiple BSides events, Boardwalk Bytes, and corporate conferences. He’s passionate about helping fast-moving teams build secure systems without sacrificing velocity.
Outside of security, Chris builds music applications and spends his free time visiting music venues around the world.
 dafinga |
dafinga |  dafinga |
dafinga |  cmaenner
—
Presenting: Securing AI Workloads in Kubernetes: Lessons from Scaling Startups
cmaenner
—
Presenting: Securing AI Workloads in Kubernetes: Lessons from Scaling Startups
Chris Ryan
No information submitted.
—
Presenting: CloudShell Abuse: a CTF, API, and persistent access to CPU/network/storage
Derek Chamorro
Derek is the Head of Security at Together.ai and the former Head of Infrastructure Security at Cloudflare. He has over 20 years of experience in designing security frameworks at scale. His main focus is on research and development within the fields of encryption and infrastructure security.
He earned a masters in cybersecurity from Purdue University and now owns more than 50 global patents related to cryptography, key management, and distributed ledger technology.
—
Presenting: It’s Not the CPU’s Fault: Adventures in GPU and Firmware Forensics
Dickson Kwong
Dickson Kwong is a Senior Information Security professional with over a decade of experience in red teaming and blue teaming. Work experience spans from financial institutions, US government agencies, and technology startups.
—
Presenting: Modernize, Vectorize, and Visualize CyberOps Data, Threat Intel with Qdrant
Erich Kron
Erich Kron, CISO Advisor at KnowBe4, author, podcaster and regular contributor to cybersecurity industry publications, is a veteran information security professional with over 30 years’ experience in the medical, aerospace manufacturing and defense fields. He is the former security manager for the US Army’s 2nd Regional Cyber Center and holds CISSP, CISSP-ISSAP, SACP and many other certifications. Erich has worked with information security professionals around the world to provide the tools, training and educational opportunities to succeed in Information Security.
 ErichKron
—
Presenting: The Chronicles of NERD-ia: Making a Smart Home That Works Most of the Time
ErichKron
—
Presenting: The Chronicles of NERD-ia: Making a Smart Home That Works Most of the Time
Grey Fox
Grey Fox is a Security Engineer and Vulnerability Rustler working on global ICS products. As a U.S. military veteran with 20 years experience, he cut his teeth in digital network intelligence, cyberspace warfare, and ground combat tactics. Grey Fox lugs baggage from numerous deployments ranging from offensive cyber operations planning and execution to military information support operations. He currently teaches Digital OPSEC, Expedient Software-defined Radio, and Tactical Emergency Casualty Care to both civilian and military groups. Grey Fox has been tolerated speaking at Def Con, various B-Sides, and other cons in addition to chairing panels on consumer data privacy for Federal research and accountability. When not seeking some free time, Grey Fox is threat modeling your AI applications and cos-playing as a Human Resistance fighter against Skynet.
—
Presenting: Going AFK – A Discussion on Standing Up and Standing Out
h00die
h00die is currently employed with nDepth Security as a senior penetration tester. Previously he helped start Exploit-DB as one of the original staff moderators for submissions and quality control experts. He is currently one of the few non-Rapid7 employees entrusted with commiter rights for the Metasploit framework, volunteering to create new module, peer review submissions, and keep the framework awesome over the last 10 years.
 h00die
—
Presenting: New Windows Persistence Techniques in Metasploit
h00die
—
Presenting: New Windows Persistence Techniques in Metasploit
 h00die
—
Presenting: New Windows Persistence Techniques in Metasploit
h00die
—
Presenting: New Windows Persistence Techniques in Metasploit Jason Blanchard
Jason Blanchard has been happily adopted into the hacker community at Black Hills Information Security (BHIS) since 2019, despite “working in marketing.” He’s held a variety of dream jobs, including teaching filmmaking, owning the world’s most famous comic book store, and supporting infosec community efforts at SANS. At BHIS, he’s often called the “Director of Excitement,” though his formal title is Content and Community Director. In his day-to-day work of “sucking at capitalism,” Jason focuses on helping others, sharing knowledge, and giving away lots of free stuff. Outside of work, he spends time with his wife and daughter and hosts workshops to help people find jobs through, “Job Hunt Like a Hacker.”
—
Presenting: Job Hunt Like a Hacker
Jenko Hwong
Jenko Hwong is a Principal Security Researcher at Huntress Labs, focusing on identity-based attacks and abuse. Prior to Huntress, he spent 6 years at Netskope Threat Labs, and has over 20 years in engineering and product roles at various security startups in vulnerability scanning, AV/AS, pen-testing/exploits, L3/4 appliances, threat intel, and windows security.
 jenkohwong
—
Presenting: CloudShell Abuse: a CTF, API, and persistent access to CPU/network/storage
jenkohwong
—
Presenting: CloudShell Abuse: a CTF, API, and persistent access to CPU/network/storage
Jerry Jones IV
Jerry Jones IV is an Associate Delivery Consultant – Security at Amazon Web Services, where he specializes in helping customers architect and implement secure, compliant cloud solutions. With extensive experience spanning federal cybersecurity, cloud security architecture, and AI/ML implementations, Jerry brings a unique perspective on building resilient systems that meet rigorous regulatory requirements.
Prior to joining AWS, Jerry served as an Information System Security Officer at the U.S. Department of Education, where he led complex Authorization to Operate (ATO) efforts for mission-critical systems, successfully navigating the transition from NIST 800-53 rev4 to rev5 and managing cybersecurity operations for systems with budgets exceeding $5 million. His federal service also includes roles at the Federal Deposit Insurance Corporation, where he administered the agency’s Cyber Security Assessment and Management (CSAM) tool and guided authorization efforts across 19 diverse divisions, and the U.S. Department of Agriculture, where he contributed to cloud migration strategies and high-value asset protection.
Jerry’s technical expertise spans cloud architecture, security automation, and AI/ML integration. He has designed and deployed enterprise-grade solutions including centralized backup and logging strategies for AWS Organizations, multi-account governance frameworks, and automated security baselines that ensure consistent compliance across distributed environments.
—
Presenting: Too Many Security Tools? ASH Has Entered the Chat
Jessie Jamieson
Dr. Jessie Jamieson is a research mathematician with almost a decade of experience applying mathematical techniques to cybersecurity and decision making.
She’s now a mathemagician (you read that right) at Turngate and an AI SME at SilverEdge Government Solutions. When not doing cyber stuff, she’s chilling with her dog, Dax, and her lovely husband, William, or perfecting her dolphin dive as a libero on a number of volleyball teams within the DMV.
 ringer.bsky.social
—
Presenting: Why Integer Factorization is F****** Hard: a History
ringer.bsky.social
—
Presenting: Why Integer Factorization is F****** Hard: a History
Joel Garcia
Husband | Father | U.S. Marine Corps Retired | nDepth Security | Alumnus of Capital Technology University & University of Maryland Global Campus
—
Presenting: New Windows Persistence Techniques in Metasploit
John Aron
I grew up with the mantra of ‘those who talk, don’t know; and those who know don’t talk,’ finding myself wading through the forests to climb outside routes. My climbing friends are astonished by the breadth and scope of the information security knowledge to defend our data and identity. Except, there is more to defend like civil liberties and civil infrastructure.
—
Presenting: Letters and more letters
Joseph N. Wilson
Joseph N. Wilson is a co-founder of QubitAC and an emeritus faculty member at the University of Florida who received his PhD in Computer Science from the University of Virginia. During his 41 year academic career, he carried out a wide variety of research projects and authored over 150 publications concerning topics including cybersecurity, machine learning, landmine detection and remediation, and computer vision. In addition to his academic work, Dr. Wilson has been a GIAC certified network and web application penetration tester as well as a malware and forensic analyst. His current work is aimed at helping organizations and people improve both their computational and communications security and privacy. He received the General Ronald W. Yates Award for Excellence in Technology Transfer for work leading to successful landmine and IED detection systems employed by US military support forces in Afghanistan.
—
Presenting: You Can’t Migrate What You Can’t See: Discovering Real Post-Quantum Crypto
Kaitlin Seng
Kaitlin has over a decade of experience as a software engineer developing cybersecurity tools with a background spanning applied research, open-source contributions, and startup innovation. Kaitlin is currently with Ginger Cybersecurity, securing Rust & Go applications on AWS.
 kaitlinseng
—
Presenting: The Case for MicroVMs: Container-Like Agility with the Security of VMs
kaitlinseng
—
Presenting: The Case for MicroVMs: Container-Like Agility with the Security of VMs
Kat Fitzgerald
Chicago-based (but soon, Porto!) and proudly a natural creature of winter, I thrive on snow, OSS, and just the right amount of chaos. Whether sipping Grand Mayan Extra Añejo or warding off cyber threats with a mix of honeypots, magic spells, and a very opinionated flamingo named Sasha (the BSidesChicago.org mascot), I keep things interesting. Honeypots and refrigerators rank among my favorite things—though my neighbors would likely disagree.
 rnbwkatt.bsky.social |
rnbwkatt.bsky.social |  infosec.exchange/@rnbwkat |
infosec.exchange/@rnbwkat |  Kat Fitzgerald
—
Presenting: Cloud Misconfigurations: Oh look – Poke, Poke,, Breach!
Kat Fitzgerald
—
Presenting: Cloud Misconfigurations: Oh look – Poke, Poke,, Breach!
Kevin Figueroa
Red Team operator with experience breaching enterprise environments through sophisticated network, web application, API exploitation campaigns. Kevin Figueroa specializes in full-scope penetration testing, living-off-the-land techniques, and custom tooling development. Passionately tracking adversary TTPs while weaponizing AI and vector databases for automated attack path discovery and payload generation to expose and close critical gaps in organizational defenses.
 KevinFigueroa
—
Presenting: Modernize, Vectorize, and Visualize CyberOps Data, Threat Intel with Qdrant
KevinFigueroa
—
Presenting: Modernize, Vectorize, and Visualize CyberOps Data, Threat Intel with Qdrant
Kiara Deloatch
I am currently working in the digital forensics and incident response space, currently pursuing a Master of Science in Cyber Operations (Red Team) with a strong academic and practical foundation in DFIR (B.S Cyber Forensics). My work and studies focus on investigative thinking, evidence-based analysis, and understanding how complex systems fail under real-world conditions. I approach emerging security problems with a practitioner mindset, grounded in the realities of incident response rather than theoretical idealism.
This talk reflects the type of problems many defenders are already encountering but do not yet have shared language or frameworks to address. As AI systems become embedded in security tooling and decision-making workflows, questions around data integrity, poisoning, and auditability are no longer hypothetical. I bring a DFIR perspective that translates existing investigative skills to these new environments without overpromising detection or claiming advanced tooling that does not yet exist. BSides has always emphasized practical knowledge-sharing and honest conversations, and this session aligns with that mission by helping the community think critically about AI risk using familiar, defensible methods.
—
Presenting: Nothing Looks Broken: Investigating AI When the Model Behaves
Mackenzie Jackson
Mackenzie Jackson grew up in a traveling circus in New Zealand (yes, really) and traded juggling fire for something even more dangerous: application security. At Aikido Security, he helps developers understand how hackers actually break things. He’s a former founder and CTO, spoken in 30+ countries, hosts The Disclosure Podcast, and still insists New Zealand makes the best coffee.
 advocatemack
—
Presenting: Worms, Tokens, and Trust: The Industrialization of Supply Chain Attacks
advocatemack
—
Presenting: Worms, Tokens, and Trust: The Industrialization of Supply Chain Attacks
Matthew Gracie
Matthew Gracie is a defensive security specialist with fifteen years of Blue Team experience in higher education, manufacturing, financial services, and healthcare. He is currently a Senior Engineer at Security Onion Solutions, as well as the interim director of the Cybersecurity graduate program at Canisius University. Matt is also the lead organizer of Infosec 716, a monthly meetup for security enthusiasts in Western New York, and the BSides Buffalo technology conference. He enjoys good beer, mountain bikes, open source security tools, and college hockey, and can be found on Bluesky  InfosecGoon.
—
Presenting: A Standard For Investigative Playbooks
InfosecGoon.
—
Presenting: A Standard For Investigative Playbooks
Nimish Sharma
Results-driven Cybersecurity Engineer with diverse experience across Healthcare, Banking, Public, and Telecom sectors, cross-functional project guidance and stakeholder support, security architecture strategy, application security, predictive analytics, and enterprise risk management. Adept at designing and implementing scalable solutions, driving automation, and delivering quantifiable value and innovation.
—
Presenting: Breaking Silos, not Systems: Dissecting the Cloud Beast and Harboring No Illusions: Navigating risks in a FaaS world
Niveadita Razdan
Niveadita Razdan is a STEM professional and fiction author with a background in global data systems, regulatory intelligence and large-scale technical problem-solving. She brings a unique narrative lens to break down the hidden risks inside serverless and event-driven cloud architectures.
—
Presenting: Breaking Silos, not Systems: Dissecting the Cloud Beast
Pujita Sahni
Pujita Sahni is a Delivery Consultant specializing in cloud security, risk, and compliance at AWS. In her role, she is responsible for architecting IAM governance frameworks and security automation solutions that enable organizations to implement secure cloud migrations and shift security left within enterprise environments.
She brings a broad technical background across identity and access management, vulnerability management, infrastructure-as-code security, and DevSecOps practices, providing a comprehensive view of how security platforms are built, automated, and maintained across enterprise cloud environments.
—
Presenting: Too Many Security Tools? ASH Has Entered the Chat
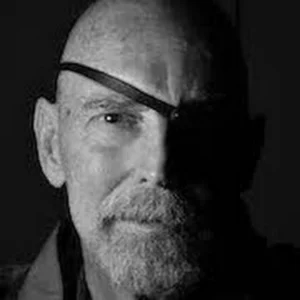
Robert M. Lee
Robert M. Lee is CEO and co-founder of Dragos, the global leader in Operational Technology (OT) cybersecurity. The Dragos Platform protects critical infrastructure and industrial operations worldwide. For the World Economic Forum, Robert is a frequent speaker and serves on the cyber resilience subcommittees for Oil & Gas and Electricity. He is a SANS Fellow and on boards for the International Society of Automation and National Cryptologic Foundation. Robert was a U.S. Air Force Cyber Warfare Operations Officer tasked to NSA, and subsequently helped lead the investigation into the 2015 attack on Ukraine’s power grid. He continues his public service as Lieutenant Colonel in the Army National Guard, designing and leading OT cybersecurity and response.
—
Presenting: Keynote
Sharon Shama
Sharon has a strong background in defensive research, especially around emerging AI technologies and GCP environments. Off the clock, she channels that same curiosity into cooking, taking on kitchen challenges like beef Wellington and lemon pie.
—
Presenting: Illuminating Shadow AI: An Open-Source Tool for CustomGPT Risk Assessment
Shawn Thomas
Shawn Thomas is the Director of Threat Detection and Response at ZoomInfo, where he spends his days building the systems and teams that find badness before it becomes a headline. With nearly 20 years of experience in security, he’s done stints across incident response, detection engineering, and security operations, basically anywhere there are fires to fight and chaos to wrangle.
In a past life he was a regular on the conference circuit and hosted some infosec podcasts, but these days he’s a recovering extrovert who prefers the company of birds to people. When he’s not hunting threats, he’s in the woods with a camera, hoping a pileated woodpecker holds still for once.
—
Presenting: Finding Badness with the Threat Detection and Response Lifecycle
Shivam Dhar
With nearly a decade of experience across sectors such as e-commerce, healthcare, gaming, open-source, and cybersecurity, within both large enterprises and agile startups, Shivam brings a creative, solutions-driven approach to complex challenges. Committed to community engagement, he actively mentors early-career cybersecurity professionals, judges prestigious tech awards, peer-reviews academic research, speaks at cybersecurity conferences, and contributes to tech-for-good initiatives with nonprofit organizations. He currently leads cloud security efforts at JPMorganChase, driving robust solutions to support the firm’s ongoing growth.
—
Presenting: Breaking Silos, not Systems: Dissecting the Cloud Beast and Harboring No Illusions: Navigating risks in a FaaS world
Steve Dyson
With a background in law enforcement and cybersecurity, Steve is highly skilled in cyber risk management, cloud security, threat mitigation, and intelligence gathering and analysis. Steve has expertise in a range of cybersecurity incident response and threat hunting tools, as well as in information security system design, management, and analysis. Steve also brings a wealth of specialized experience in both Healthcare and Financial Services sectors and has a legal background focused on regulatory compliance and digital privacy.
—
Presenting: Aligning Cyber Defense and Compliance
Stryker
Stryker is the director of content and threat analysis at Fable Security, where she translates technical research and qualitative intelligence into the “so what?” and “what now?” solutions that keep more people safe and secure. Before Fable, she produced threat intelligence for GEICO, Blackpoint Cyber, and other cybersecurity vendors. You can often find her playing “Backdoors & Breaches” in the hallway after her talks at DEF CON, SecTor, and Bsides conferences around the United States. Stryker lives in Baltimore, growing parsley for butterflies and algae for shrimp.
—
Presenting: Just a TIP: DIY Your First Threat Intelligence Platform
Sweta Deivanayagam
Sweta Deivanayagam is a cybersecurity professional with 15 years of experience protecting software and computer systems from hackers and security threats. Currently working as a Lead Security Engineer at Salesforce, Sweta designs and builds security solutions to keep their software safe throughout the entire development process, especially when using cloud technology and AI.
Before joining Salesforce, Sweta spent 10 years working as a security consultant, first at Cigital and then at Synopsys. In these consulting roles, Sweta served as a security detective and advisor, examining other companies’ software applications to find vulnerabilities and weaknesses that hackers could exploit.
Sweta used specialized tools to scan code for security flaws, tested applications by attempting to break into them legally, and then helped development teams fix these problems. Throughout her career, Sweta has also helped companies set up automated security systems in their software development processes, created training programs to teach developers how to write more secure code, and provided strategic guidance on improving overall security practices. Sweta’s expertise spans a wide variety of security tools and technologies, from code analysis software to penetration testing tools, helping organizations build stronger and more secure applications and systems.
—
Presenting: Using AI in Threat Modeling
Teddy Katayama
Kaoru T. “Teddy” Katayama is the Chief Technology Officer and co-founder of Exploit Strike, where he leads offensive security operations and defines the technical strategy behind the firm’s penetration testing and adversary simulation engagements. With nearly two decades of experience in cybersecurity, Teddy blends deep technical expertise with a practical focus on real-world risk.
His interest in security began early. At age ten, he bypassed his elementary school’s door-lock system, and by eighth grade he had built a Java-based port scanner. In high school, his skills earned multiple SkillsUSA awards in network management and remote administration.
Teddy holds a Bachelor of Science in Computer Engineering and a Master of Engineering in Cybersecurity from the University of Delaware and is currently completing his Ph.D. in Electrical and Computer Engineering, specializing in cybersecurity and machine learning. His research focuses on applying machine learning to threat detection and security operations and has been supported by a $259,527 research grant from Cisco Systems.
Teddy has led security initiatives for organizations ranging from startups to large enterprises. Prior to Exploit Strike, he co-founded Golden Egg Labs, created the University of Delaware’s first VIP Red Team, and led penetration testing and compliance projects across the Mid-Atlantic. He also worked at Cisco Systems, developing machine learning tools for detecting malicious binaries in encrypted traffic.
—
Presenting: Hidden Exposure Crisis – How Supply Chain Leakage is Becoming the Norm
TheClockworkBird
I am TheClockworkBird, and I have been a part of the Cicadasolvers community for nearly 6 years. I like to think of myself as a kind of tour guide for the digital interactive museum that is Solvers, and with day job as a Maryland educator, this role of digital docent suits me well.
With a background in anthropology, my solving expertise lies in the realms of art, literature, and the sociological aspects of the puzzle. I work as a community organizer for Cicadasolvers, putting together solving sessions, curating collaboration between solvers, and guiding newcomers through the vast materials pertaining to the puzzle. Over the last three years my work has come to include the tracking and tamping of misinformation as it relates to cicada, utilizing lessons learned from teaching in order to navigate the info-rich domain of 3301 and their puzzles.
In the end, bringing curious cryptanalysis fiends and all in betweens together is what I like to do!
 theclockworkbird.bsky.social |
theclockworkbird.bsky.social |  mastodon.social/@theclockworkbird
—
Presenting: The Misinformation Misadventures of Cicada 3301
mastodon.social/@theclockworkbird
—
Presenting: The Misinformation Misadventures of Cicada 3301
Tim Pappa
Tim Pappa is an Incident Response Engineer – Cyber Deception Strategy, Content Development, and Marketing, Cyber Deception Operations, Walmart Global Tech. Before Walmart Global Tech, Tim was a Supervisory Special Agent and profiler with the Federal Bureau of Investigation’s (FBI) Behavioral Analysis Unit (BAU), where he specialized in cyber deception and online influence. Tim has presented and published at various academic and industry conferences, including Black Hat Asia, NDSS, IEEE S&P, CYBERWARCON, and the Honeynet Project. Tim has also held various strategy and policy Fellow roles at the Center for Strategic and International Studies (CSIS) and the Aspen Institute. Tim’s current research interests include attitudes toward cybercriminal felons, HoneyContent, and cyber deception design thinking. Singapore-based publisher World Scientific published his first book, “Influencing the Influencers: Applying Whaley’s Communication and Deception Frameworks to Terrorism and Insurgent Narratives” in summer 2025. He is currently writing No Starch Press’s first book on cyber deception.
 Tim Pappa
—
Presenting: The Heart Wants What It Wants: Convenience and Moral Drift in Cybercrime
Tim Pappa
—
Presenting: The Heart Wants What It Wants: Convenience and Moral Drift in Cybercrime
Vladimir Drinkman
No information submitted.
—
Presenting: The Heart Wants What It Wants: Convenience and Moral Drift in Cybercrime